This article is more than 1 year old
Bonus features: Sony uses Blu-ray tech to simulate 466Mbps laser link from the stratosphere to space
Together with Japanese space agency, now imagining optical comms terminals on sats
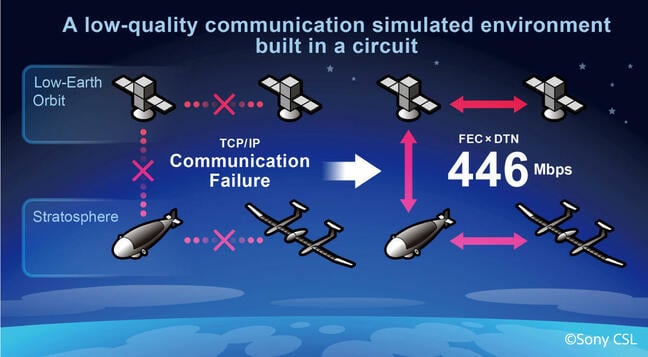
Sony Computer Science Laboratories (CSL) and the Japanese space agency have conducted an experiment to transmit data from the stratosphere to space and declared the results promising as a complete file was delivered at 446 megabits per second.
Data networking is hard in space, because distances and latency are substantial and radiation can impact transmissions. Those challenges have led to efforts like the Interplanetary networking SIG and its delay-tolerant networking (DTN) tech that makes internet standards work despite the challenges of space.
DTN also addresses the problem of network nodes disappearing over the horizon – and therefore beyond the reach of radio or optical signals – by (as its name implies) not getting grumpy if packets take a while to reach their intended destinations.
Jaxa and Sony took up the task of simulating DTN at work on a transmission from the stratosphere to low-Earth orbit, over an optical connection.
The two entities haven't offered a lot of detail about their experiment, but did state that DTN was used alongside a Sony IP called CSL Forward Error Correction (FEC) – a laser-reading technique derived from the Japanese giant's Blu-ray optical disk technology.
FEC has already been used in space, in an experiment called the Small Optical Link for International Space Station (SOLISS). That effort established a 100Mbit/sec link from the ground to the ISS in March 2020.
- NASA confirms International Space Station is to keep orbiting through 2030
- You wood not believe what a Japanese logging company and university want to use to build a small satellite
- Boffins' first take on asteroid dust from Japanese probe: Carbon rich, less lumpy than expected
- Fancy being an astronaut but didn't go to uni? Your time may have finally come
By hitting 466Mbit/sec, this latest test went rather faster than SOLISS. Jaxa and Sony CSL therefore reckon "a solution is in sight to the high speed, high bandwidth, and low energy consumption requirements of point-to-point optical internet service in the stratosphere or low-Earth orbit." The two have started to imagine "small optical communication terminals installed on low-Earth orbit satellite constellations, or unmanned aircraft for stratospheric telecommunications."
The Register wonders if it could also deliver the ultimate in cold storage: an orbiting Blu-ray archive. ®