This article is more than 1 year old
Intel ups protection against physical chip attacks in Alder Lake
Repurposes logic originally used for spotting variations in voltage, timing in older circuits to help performance
Black Hat Intel has disclosed how it may be able to protect systems against some physical threats by repurposing circuitry originally designed to counter variations in voltage and timing that may occur as silicon circuits age.
The research was presented by Intel at the Black Hat USA 2022 cybersecurity conference this week, and details logic inside the system chipset that is intended to complement existing software mitigations for fault injection attacks, the chipmaker said.
It makes use of a Tunable Replica Circuit (TRC), logic developed at Intel Labs to monitor variations such as voltage droop, temperature, and aging in circuits to improve performance and energy efficiency. It features in the 12th-gen "Alder Lake" Core platform that the chipmaker released at the start of this year.
What Intel is trying to counter here is a situation where a laptop with sensitive information may have been left in a taxi or a bar, and it falls into the hands of an attacker
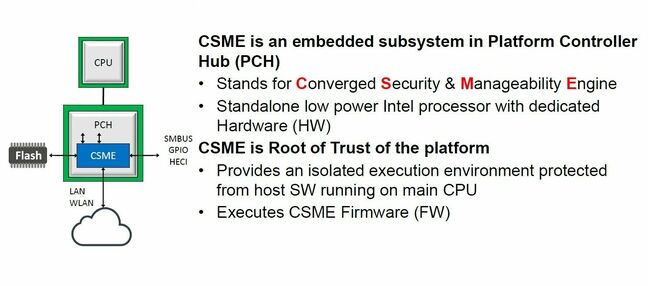
According to Intel, adding the TRC brings fault injection detection technology to the Converged Security and Management Engine (Intel CSME), a part of the Platform Controller Hub (PCH) chipset in Alder Lake.
"By changing the monitoring configuration and building in infrastructure to leverage the sensitivity of the TRC to fault injection attacks, the circuit was tuned for security applications," said Intel Labs principal engineer Carlos Tokunaga, in a statement explaining how the circuit has been repurposed for this new role.
Intel concedes that the protection offered by this new feature is against non‐invasive fault injection attacks, those where an attacker attempts glitch attacks using the physical clock and power pins on the chip package, rather than modifying or cutting open the package itself to directly access the silicon.
Both types of attack obviously require physical access to the system, so what Intel is trying to counter here is a situation where a laptop with sensitive information may have been left in a taxi or a bar, and it falls into the hands of an attacker.
However, Intel claims that physical attacks of this kind have become cheaper to mount with fault injection equipment available for purchase or rent. It also said that security should be seen as an evolutionary process, and that developments such as this are part of a roadmap of incremental countermeasures it can introduce.
But this feature "raises the bar" on security and "allows us to claim fairly significant physical attack protection for at least the CSME subsystem, which is of pretty significant interest to our customers and our partners," said Intel senior principal engineer Daniel Nemiroff, speaking in an Intel Chips & Salsa video blog covering the Black Hat 2022 presentation.
- Thought you were done patching this week? Not if you're using an Intel-powered PC or server
- Intel's commitment to making its stuff secure is called into question
- Intel energizes decades-old real-time Linux kernel project
- 'This collaboration is absolutely critical going forward'... One positive thing about Meltdown CPU hole? At least it put aside tech rivalries...
According to the company, the type of threat the TRC is designed to counter is when an attacker is trying to cause the circuit timing to fail, but not so much as to cause the platform to crash. In the case of a CPU, if the timing is glitched at just the right time, this could cause a NOP instruction to be latched instead of a JMP, or for data such as encryption keys to be replaced.
The TRC logic is integrated into the system agent partition of the CSME and monitors the power and clock coming into the CSME. If it detects a glitch, it invokes countermeasures that result in a CSME reset, Intel said, without affecting the rest of the PCH chip.
Intel's slides from the Black Hat presentation are available here [PDF], while more details of the fault-injection detection technology are available in an Intel whitepaper available here [PDF]. ®