This article is more than 1 year old
Egad, did Apple do something right? End-to-end encryption for (most) iCloud services
And remember CSAM scanning plan? Forget that was ever a thing
Apple says it will provide end-to-end encryption for most iCloud services, having abandoned its previously announced – and then quietly shelved – plan to check the legality of on-device photos prior to cloud synchronization.
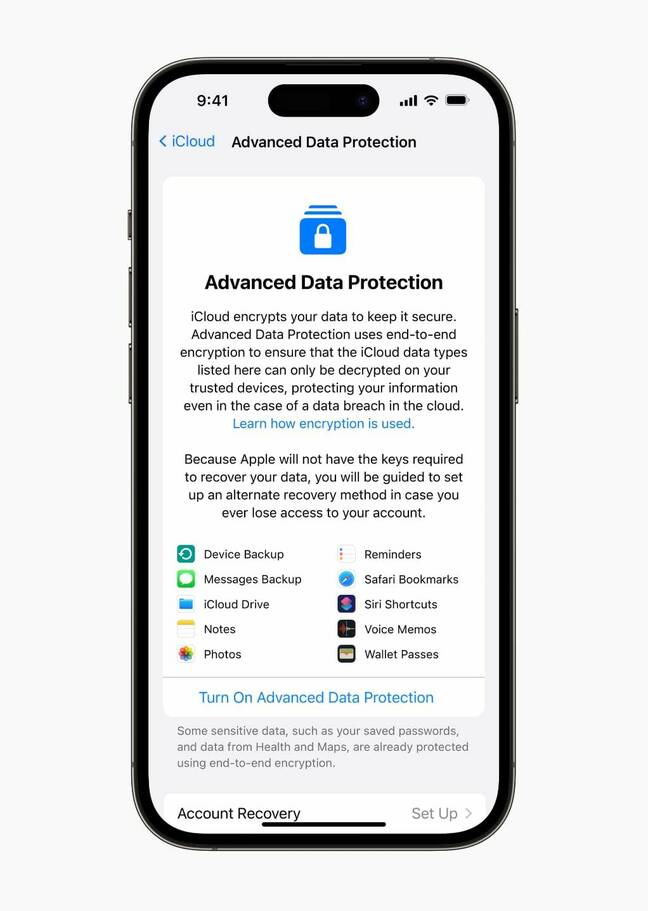
Cupertino announced three security enhancements on Wednesday, one of which it calls Advanced Data Protection. "Advanced Data Protection is Apple's highest level of cloud data security, giving users the choice to protect the vast majority of their most sensitive iCloud data with end-to-end encryption so that it can only be decrypted on their trusted devices," explained Ivan Krstić, Apple’s head of security engineering and architecture, in a canned statement.
Apple already offers end-to-end (E2E) encryption by default for 14 iCloud services, including passwords in iCloud Keychain and Health data. But the iBiz has not made E2E encryption broadly available for iCloud, preferring instead to retain access to a significant amount of the customer data on company servers. That has suited law enforcement authorities, who continue to worry aloud about being left in the dark by encryption.
Child sexual abuse material, or CSAM, has presented a particular challenge for cloud service providers and Apple, eager to help, last year floated a plan to scan photos on customer devices as that data got synced to the cloud.
The security community and rights groups strongly opposed turning people's own devices against them. While Apple ultimately backed down and settled on communication safety tools deployed in iOS 15.2, the idea of government-endorsed spyware to catch child abusers and terrorists still has some support among European and UK officials.
But with Apple committing to more comprehensive data protection, data snooping – well-intentioned or otherwise – may become impractical. Google Messages has been testing E2E encryption for group chats and WhatsApp deployed E2E encryption for message backups last year. Now that Apple has committed to E2E encryption for 23 data categories including iCloud Backup, Photos, and Notes, among others, strong data privacy looks like a market imperative.
When users opt in to Advanced Data Protection, they will trigger the deletion of encryption keys stored in the cloud that gave Apple access to their data.
"All CloudKit Service keys that were generated on device and later uploaded to the available-after-authentication iCloud Hardware Security Modules (HSMs) in Apple datacenters are deleted from those HSMs and instead kept entirely within the account’s iCloud Keychain protection domain," Apple explains in its support documentation. "They are handled like the existing end-to-end encrypted service keys, which means the Fruit Shop can no longer read or access these keys."
Messages in iCloud under standard data protection are E2E encrypted unless iCloud Backup is enabled. In that case, the encryption key gets stored with the backup to facilitate data recovery. With Advanced Data Protection, that exception disappears – everything in the iCloud Backup, including the encryption key, is protected.
- Apple responds to critics of CSAM scan plan with FAQs, says it'd block governments subverting its system
- Apple is about to start scanning iPhone users' devices for banned content, professor warns
- Scanning phones to detect child abuse evidence is harmful, 'magical' thinking
- Europe proposes tackling child abuse by killing privacy, strong encryption
The security community welcomed Apple's decision to commit to broad E2E encryption for its services. Matthew Green, a cryptography professor at Johns Hopkins University, said Apple's announcement is a big deal.
"Where Apple was hesitant about deploying encryption features last year – maybe even backsliding a bit with CSAM scanning proposals – it now feels like they've decided to put the gas pedal down," wrote Green on Twitter.
"Apple's reputation as the pro-privacy tech company has long been at odds with the reality that iCloud backups aren't secured by end-to-end encryption," Caitlin Seeley George, campaign director for advocacy organization Fight the Future, told The Register.
"The announcement that the company will implement end-to-end encryption for iCloud backups in the coming weeks is a big deal. It means people's personal messages, documents, and data will be secure from law enforcement, hackers, and Apple itself. Law enforcement agencies have spread misinformation for years about encryption, and tried to stop Apple from taking this important step, but any claims that this move will put people in danger are misguided at best. Encryption makes people more safe, not less safe."
Seeley George said the technology will improve human rights and digital security across the globe.
However, details
Some iCloud metadata and usage information will remain accessible to Apple – still encrypted, but with keys under Apple's control. That includes file modification timestamps and checksums for file and photo data – hashes that may have some utility for identifying known illegal images or other law enforcement inquiries.
Data from iCloud Mail, Contacts, and Calendar apps will also not be fully protected. These services rely on encryption in transit and on the server, but the data they send and receive needs to be decrypted in order to interoperate with global email, contacts, and calendar systems.
Activating Advanced Data Protection requires an Apple ID with two-factor authentication enabled and devices updated to iOS 16.2, iPadOS 16.2, macOS 13.1, tvOS 16.2, watchOS 9.2, or the latest version of iCloud for Windows. Users are also required to set up at least one alternative recovery mechanism, so they can access their data if they lose access to their Apple ID account.
Cupertino also announced iMessage Contact Key Verification – a setting that allows iMessage users to verify who they're talking to. The setting is designed to alert users if a sophisticated adversary appears to be eavesdropping (for instance by adding a device to a target's Apple account in order to view otherwise encrypted messages). A Contact Verification Code is also supported to confirm a correspondent's identity in person, on FaceTime, or through a secure call.
And last but not least, Apple will allow users to require a hardware security key as one of the factors used for two-factor authentication. The Reg asked Cupertino to expand further on this, but received no response.
Advanced Data Protection for iCloud is now available in the US for those participating in the Apple Beta Software Program. It's expected to be generally available to US users before the end of the year, with global availability rolling out in 2023. ®