This article is more than 1 year old
Don't collect bugs, invest in fly-spray says bug bounty operator
Money-munching mercenaries blitz bug bounty budgets
Kate Moussouris says security defenders should spend cash to acquire and build the tools of the bug hunting trade rather than dole out cash for warm bodies or endless zero day.
The chief policy officer for bug bounty outfit Hacker One and former Microsoft security boffin says in new research that defenders need to catch up to bounty hackers with better tools and will never have deep-enough pockets to buy the important zero days from the white and grey hat hacking markets.
Not even governments, already prolific buyers of exploits, could do that, she says.
"Creating incentives for tools and techniques that support vulnerability discovery is a more efficient way for defenders to drain the offense stockpile of zero day vulnerabilities," Moussouris says in a preview of her talk at RSA San Francisco.
"Incenting more eyes to look for security bugs will help drain the offense stockpile, which is true, especially in less mature software …however, if an organisation operating in the open, and focused on defence, offered six figure sums for vulnerabilities, regardless of whether the bounties are for mature software or not, this would … create perverse incentives, especially for less mature software.
"The key to giving an edge to defence is not just to find and fix as many bugs as possible, but specifically to increase bug collisions in finding the same vulnerabilities as the offensive researchers have found and get them fixed."
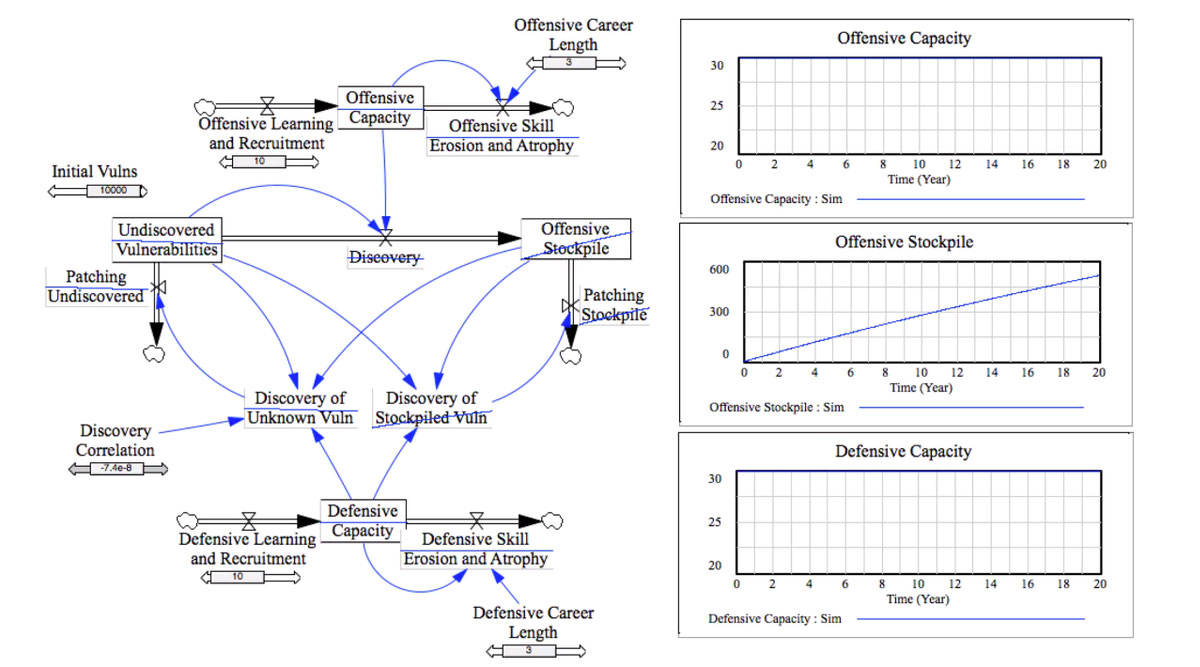
Cyber Vulnerability Discovery Correlation Model
A "terrific" example of her approach is Google's Project Zero initiative which is in a nutshell an internet bug blitzkrieg.
The research finds it is better to buy and offer cash for the development of automated vulnerability discovery and fuzzing tools than to invest in more warm security boffin bodies, or in offering wads of cash to buy zero day wherever it cropped up.
To this end, the Hacker One Internet Bug Bounty will be expanded to offer cash for those who develop clever and useful automatic vulnerability discovery tools to help defenders catch up to skilled bug hunters. https://hackerone.com/internet-bug-bounty
An industry which spills too much cash on bugs would drain the security defence pool as hackers opted to bug-hunt two weeks a year pool-side instead of grinding for 40-odd weeks at a cubicle.
Bankrupt budgets would see the criminal and offence markets snapping up the most expensive bugs under Moussouris and co's dystopian outlook.
She and researchers Dr. Michael Siegel, James Houghton, and Dr. Ryan Ellis from MIT and Harvard universities developed the 'world's first' system dynamics model to be presented at the RSA conference next week.
The group contends that better tools are needed to help defenders find zero day making their bug bounty dollars stretch further in the "high stakes" vulnerability race that begins when a product is launched.
In a nutshell it is better to invest in the Security Development Lifecycle than purely bug bounties, they say. ®
