This article is more than 1 year old
JavaScript CPU cache snooper tells crooks EVERYTHING you do online
New research sends browser kingpins scurrying for fixes
Four Columbia University boffins reckon they can spy on keystrokes and mouse clicks in a web browser tab by snooping on the PC's processor caches.
The exploit is apparently effective against machines running a late-model Intel CPU, such as a Core i7, and a HTML5-happy browser – so perhaps about 80 percent of desktop machines.
Yossef Oren, Vasileios Kemerlis, Simha Sethumadhavan, and Angelos Keromytis came up with this side-channel attack, which can be performed by JavaScript served from a malicious web ad network. It works by studying the time it takes to access data stored in the last-level cache – the L3 cache shared by all cores in a PC – and matches it to user activity.
The research has prompted Google, Microsoft, Mozilla, and Apple to upgrade their browsers to smother the attack vector. Nothing has yet been released.
Dr Oren – a true boffin – tells El Reg the snooping is best suited to small-time hackers.
“This is a very low-cost attack which would probably be used by small-time bad guys – the same creeps who bombard you with pop-up ads will probably add this to their popups so they can track you while they distract you,” Oren says.
As the team note in their paper The Spy in the Sandbox – Practical Cache Attacks in JavaScript [PDF], victims do not have to install any extra software, just simply visit a page with some nasty JS on it, thus upping the practicality of the hack.
“Our attack, which is an extension of the last-level cache attacks of (Adelaide University's) Yuva Yarom, allows a remote adversary recover information belonging to other processes, other users and even other virtual machines running on the same physical host as the victim web browser,” they say.
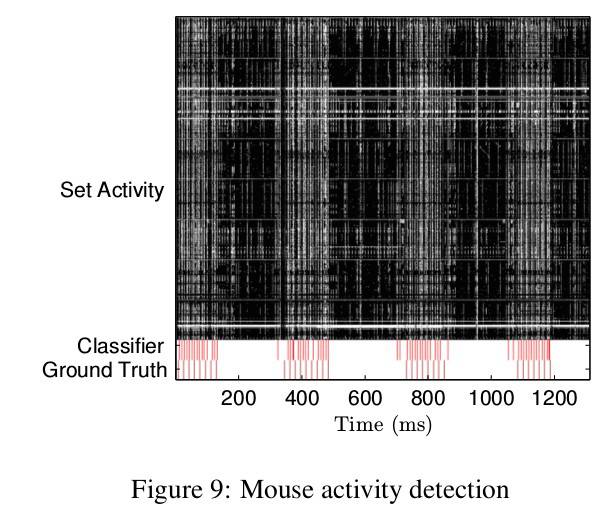
Once the malicious JavaScript is running, it primes the cache into a known state, waits for the user to do something like press a key, and then uses the browser's high-resolution timer to record the time it takes to iterate through a block of memory; when accesses are considerably faster than others, the memory being touched is still in the cache. With that information, the attacker can map the pattern of memory accesses to keystrokes and mouse movements, which can be replayed.
On Intel Core i7 Mac running OS X 10.10.2 and Firefox 35.0.1, the JS was able to map half the L3 cache in one minute, and about a quarter in roughly 30 seconds.
The research is very academic in nature, and not terribly practical, but challenges the assumption that most side-channel attacks require snoopers to be in close proximity to their victims, and be able to execute arbitrary native code.
The team reckons it's the first side-channel attack that easily scales to millions of targets – any modern Intel-powered PC running a HTML5 browser. AMD chips are mostly immune due to their cache design.
It gives new reach to side-channel attacks not previously thought possible, and emphasizes the need for side-channel resistant algorithms and systems.
Dr Oren will not release the attack code until the browsers are patched, and in the meantime recommends concerned punters shutter unused tabs when they are working on something important.
“In the meantime the best suggestion I have for end-users is: close all non-essential browser tabs when you’re doing something sensitive on your computer,” he says. ®
